Phishing Protection: The Default Browser Is Critical
Using increasingly sophisticated methods, scammers are trying to steal credentials from unsuspecting Internet users. Make Cliqz your default browser to protect yourself from such scams. Cliqz is four times more efficient!
Every day, phishing attacks target gullible Internet users. Criminals use email and social media messages to lure users to fraudulent web sites in order to steal confidential information such as passwords and credentials.
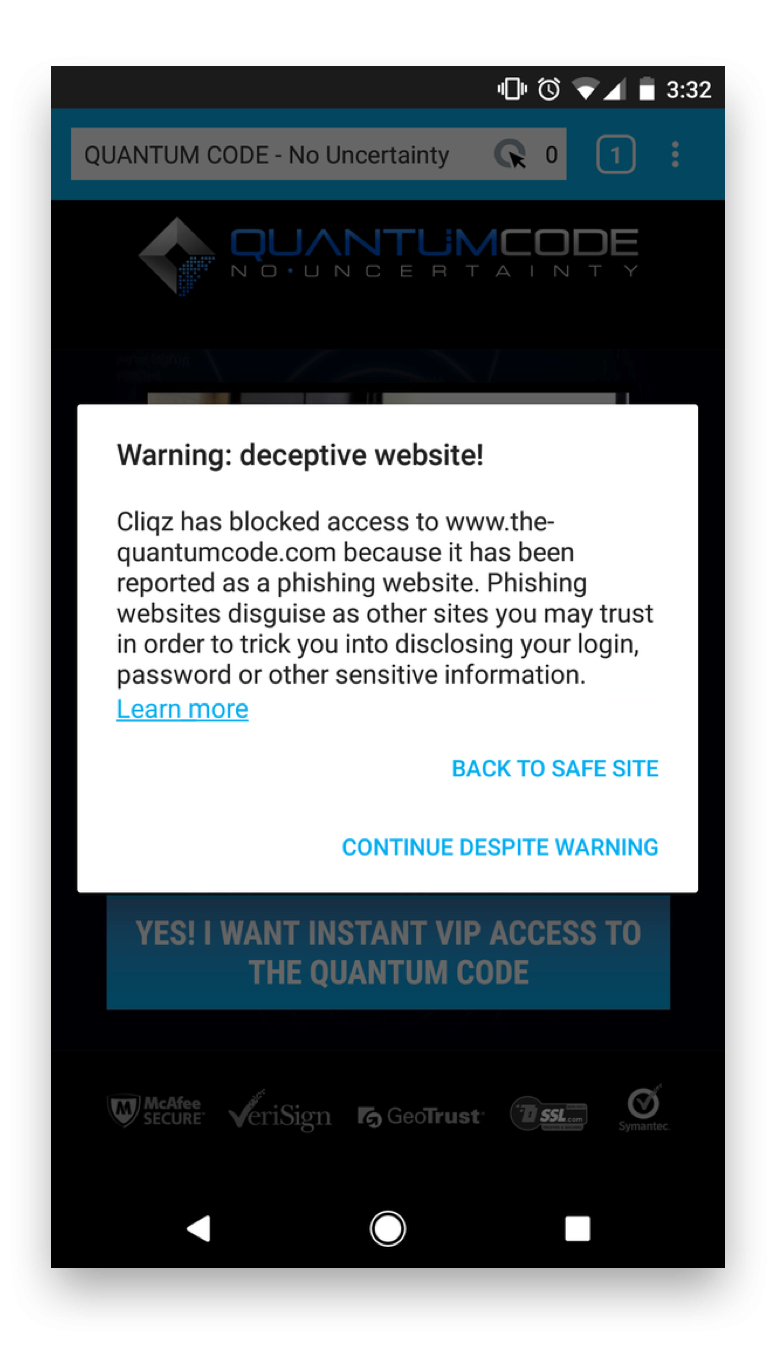
Make Cliqz your default browser now. This is the only way to benefit from its highly efficient phishing protection! How to make Cliqz your default browser on Windows 10, you can learn in this tutorial. Illustrated step-by-step guides are also available for Mac and Android. Due to Apple’s system limitations, it is not possible to change the default browser on iOS.

The Sneaky Tricks Scammers Use to Fool You
The term “phishing”, by the way, is a homophone of fishing, and is so named probably because phishing scams use lures to catch unsuspecting victims. Like tricksters at the front door or on the phone, phishers like to pretend in their messages to have a personal relationship with their victim or make false promises, such as a lottery win or free offers. By means of this so-called social engineering, they try to win the trust of the recipients.
To make their victims follow their instructions voluntarily, they build up pressure by signaling an urgent need for action (otherwise your data will be lost) or uttering concrete threats (your account will be blocked). Often scammers also impersonate a reputable bank or company. In their name they claim, for example, that for security reasons the user must confirm his login data or that the email attachment contains an invoice or order confirmation.
Many phishing mails nowadays appear deceptively genuine both visually and in terms of content, which is why careless people follow the contained link to fake login pages or malicious websites or open an attachment infected with malware. Then the scammers have already achieved their goal.
Identify Fraudulent Messages
Besides a default browser with anti-phishing functionality, the best protection against fraud attempts is vigilance and a healthy level of scepticism. Check regularly to see if you know the sender of a message and if it is really the same. You should also ask yourself whether the subject and message text make sense and whether you expect the sender to attach an item such as an invoice.
If an email seems strange to you, you should not open it, but delete it without reading it. If in doubt, you can also call your bank or the respective company to find out whether the message actually came from them.
Be especially careful when confidential data such as credit card numbers, PINs or transaction numbers (TANs) are requested in messages. Trustworthy companies would never request such information in this way. Another warning signal is an urgent request to follow a link or open an attached form.

Steps to Take If You’ve Fallen Victim to a Phishing Scam
Unfortunately, there is no such thing as 100% protection against phishing and malware, which is why you should always be cautious. It is generally recommended to use a security software and always keep it up to date, such as your operating system, browser and other applications.
If you have become the victim of a phishing attack despite all precautions, you should report the fraud as soon as possible to the provider whose name has been misused. You should also make sure that the scammers cannot use the stolen data to cause any further damage: For example, change all your passwords, block your TAN list and bank accounts if necessary, and check your online accounts (banking, shopping) regularly for unusual transactions.
Make Cliqz your default browser and benefit from its highly efficient phishing protection:




